Hi.
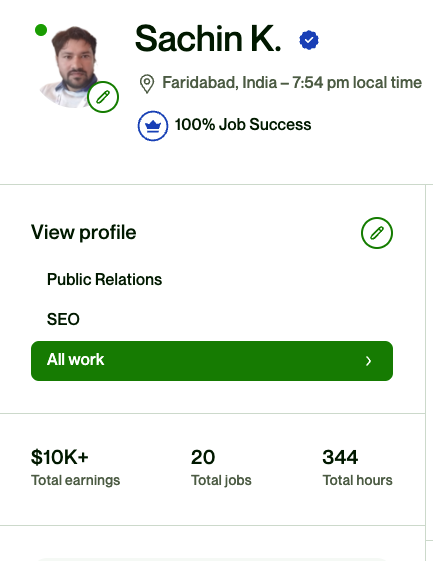
My name is Sachin Yadav. Reputation Management & SEO Expert
Boost Your Website’s Performance with a Result-Oriented SEO Consultant/Expert. Rank No. 1 on Google with Our Quality Link Building Service. Improve Your Organic Ranking and Traffic in Record Time with Contextual Links from High DA Sites
Clients & Brands I Work With





I'm a highly-qualified professional who excels in developing SEO strategies and link building. With my proven track record, I've successfully ranked highly competitive keywords

About Me
I am a qualified SEO professional with 10+ years of experience in SEO & Link Building.
I bring a wealth of expertise to the table, including online reputation management, white hat SEO, manual outreach link building, blogger research and outreach, and competitor’s link research.
My Experience
With over a decade of experience, I’ve worked across multiple niches, including Health, Tech, Insurance, Food, Travel, Education, and Hotel
My track record speaks for itself – I’ve successfully managed link building campaigns for top companies like urbanladder.com, Adobe, Wondershare Filmora, speedcheck.org/, BYJU’S, apnapaisa.com, Tata Capital, Nykaa Fashion. Plus, I’ve ranked highly competitive keywords such as Compare Term Insurance, Compare Health Insurance, Compare Child Insurance, Buy Weighing Machine, and many more medium competition keywords.
2016
Full Time SEO & ORM Freelancer on Upwork
I have a proven track record of managing successful link building campaigns for top companies like urbanladder.com, Adobe, Wondershare Filmora, speedcheck.org/, BYJU’S, apnapaisa.com, Tata Capital, Nykaa Fashion, and many more.
2015
Lemonpeak.com
Our main focus is on tech support and lead generation in the US market, using pop-ups and search networks like Google AdWords and Bing.
2014
PolicyX.com
I’ve successfully ranked highly profitable keywords such as Compare Term Insurance, Compare Health Insurance, Compare Child Insurance, resulting in a remarkable increase in website traffic from 5k to 20k in just 4 months.
2012
Healthgenie.in
I have managed SEO for the company’s website and ranked high competition keywords like Buy Weighing Machine, Buy Whey Protein, and so many others.
Client Testimonials

Reputation Management
reputation management
Link building
Link building
Blogger outreach
Blogger outreach
Negative link suppression
Negative link suppression
Guest Posting Services
Our specialized blogger outreach services can provide your website with high-quality backlinks, which are essential for improving your search engine rankings. By using our service, you can effectively boost your website’s authority and visibility.
Our quality link building service can help you achieve the top spot in Google search rankings. We only build contextual links from high DA sites, ensuring rapid organic ranking improvement and increased traffic. All our links are white hat and spam-free.
I have around 1000+ guest post sites on a variety of niches like health, Technology, Home Improvement, Finance/Business, Fashion, Travel, Education, Auto, Sports, Casino, gambling, family, entertainment, Law, Food, Dating, Shopping, Real estate etc. All blog DA Start from 20 to 80 DA.
DA 30+
Low Tier-
Niche Relevant
-
Ahrefs DR30+
-
500+ Words Expert Content
-
1000+ Organic Traffic
DA 40+
Medium Tier-
Niche Relevant
-
Ahrefs DR40+
-
1000+ Words Expert Content
-
8000+ Organic Traffic
Enter your title
Enter your description-
Niche Relevant
-
Ahrefs DR50+
-
1000+ Words Expert Content
-
5000+ Organic Traffic
Latest from Technologers
Dominate search engines with organic white hat SEO strategies by hiring a freelance SEO expert and consultant in Delhi, Noida, and Gurgaon. Contact us now to boost your online presence.

Verify OTP Online
Get a fake Indian mobile number for SMS verification with Technologers. Easily bypass phone number verification on any app or website and protect your privacy.

9 Best Anime Like Kiss X Sis
Discover the best anime like Kiss x Sis on Technologers. Find similar shows with steamy, romantic storylines and hilarious moments for your next binge-watch.

Highly Compressed Android Games under 50mb
Enjoy gaming on the go with our highly compressed Android games under 50MB. Download for free and play without compromising on quality or fun